Step 7 — As-Built Docs
Architecture (As-Built)
Section titled “Architecture (As-Built)”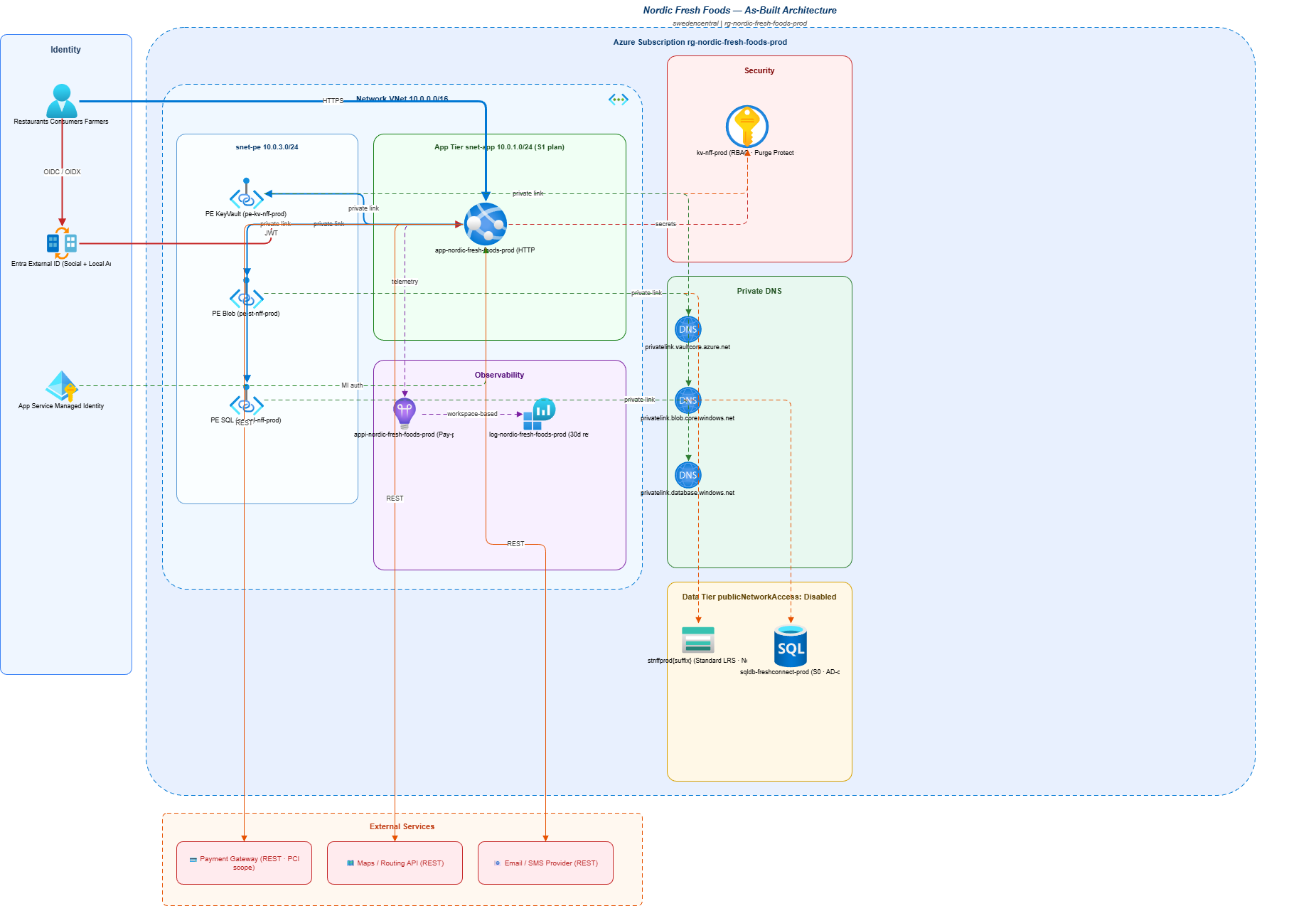
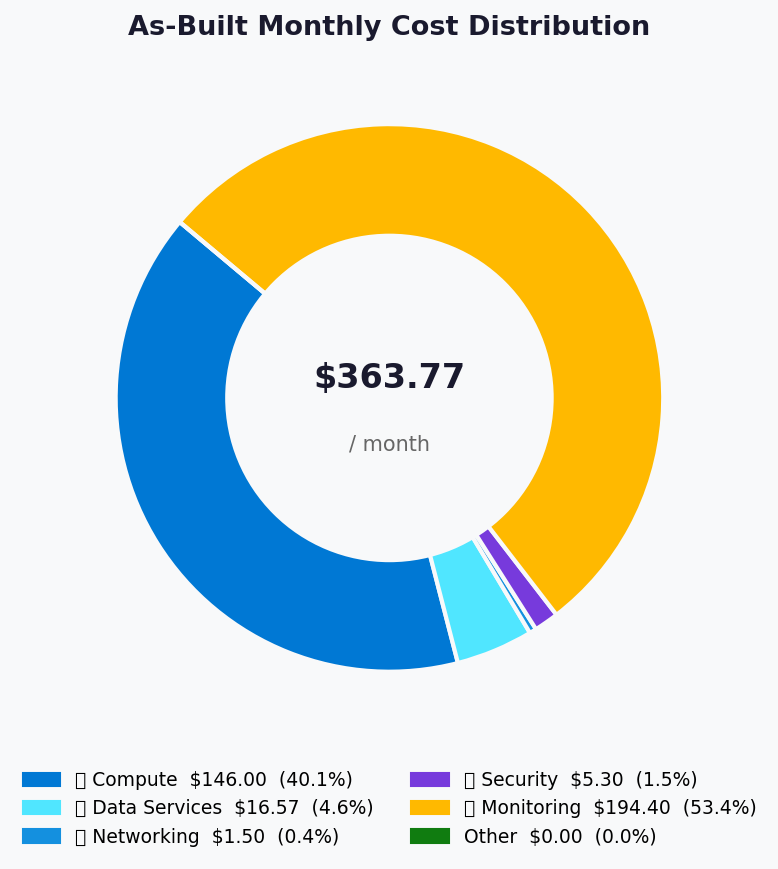
Cost Distribution (Actual)
Section titled “Cost Distribution (Actual)”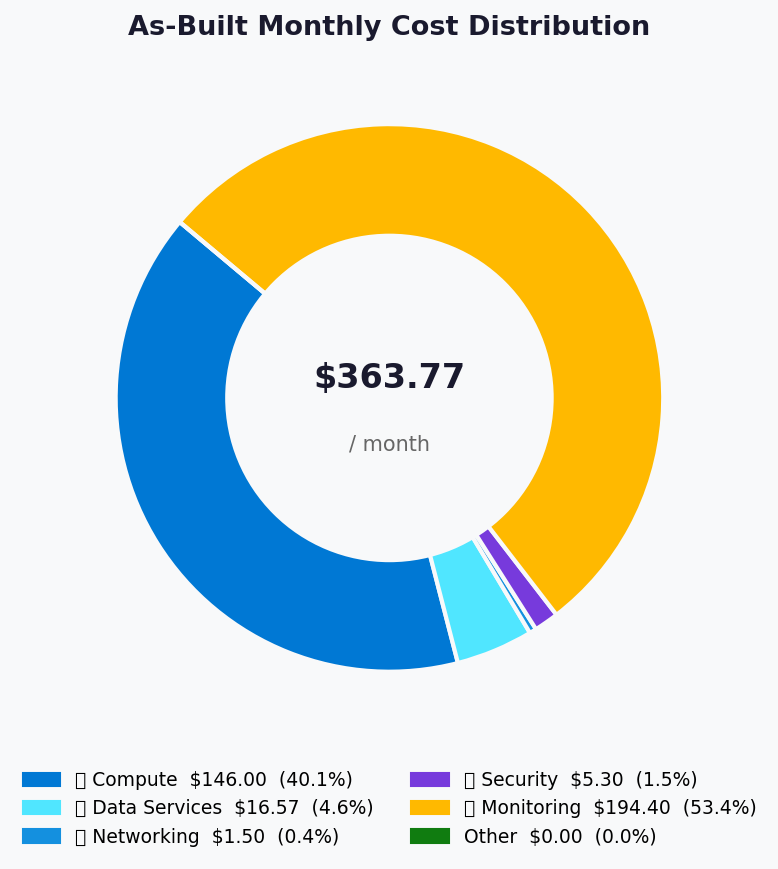
Cost Comparison (Estimated vs Actual)
Section titled “Cost Comparison (Estimated vs Actual)”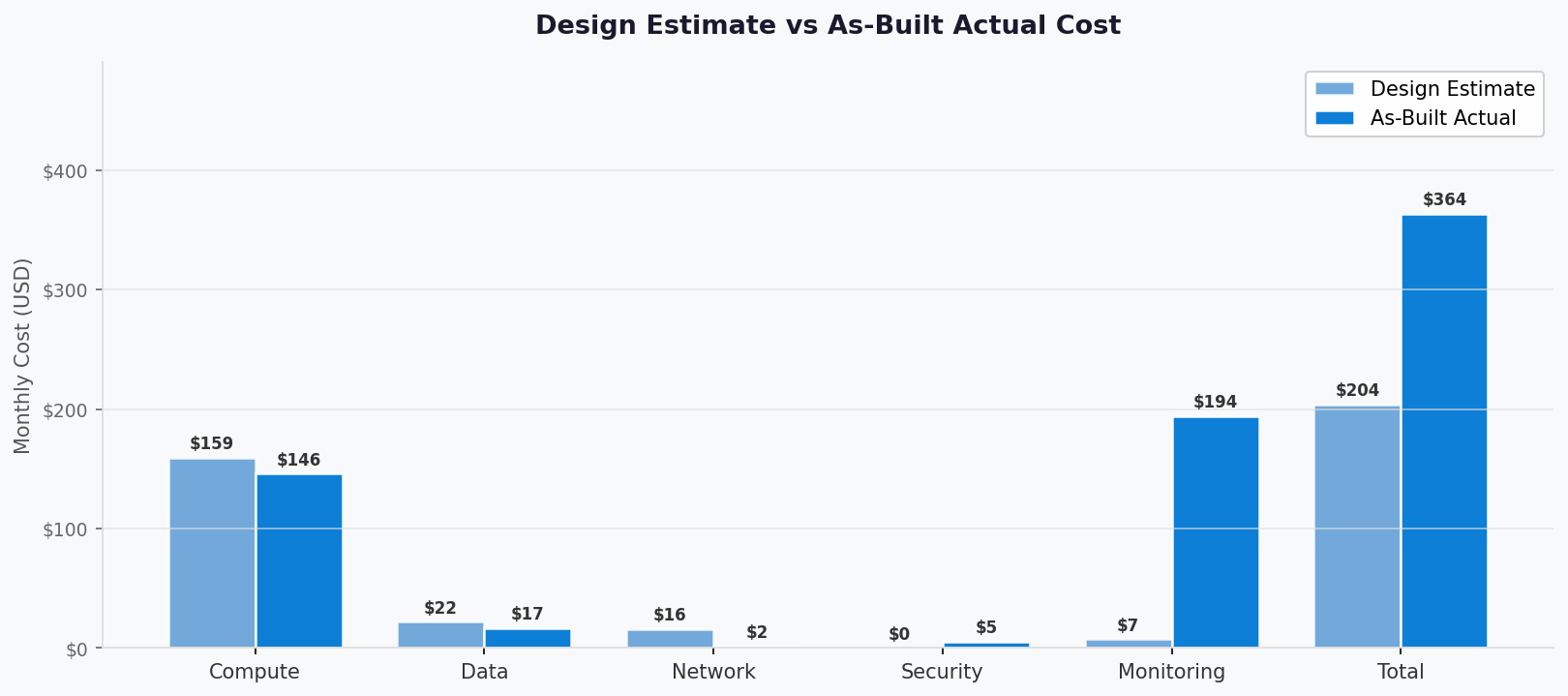
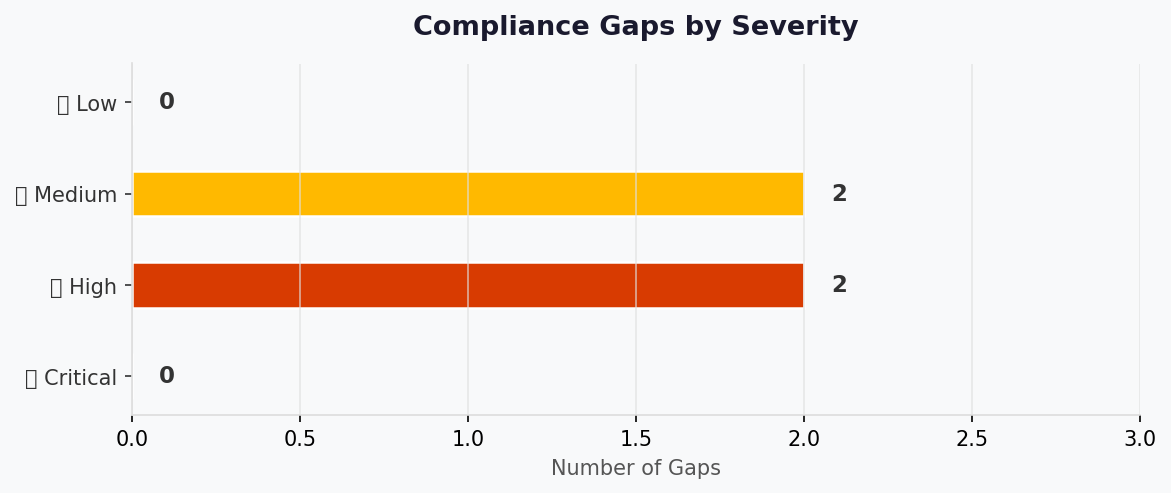
Compliance Gaps
Section titled “Compliance Gaps”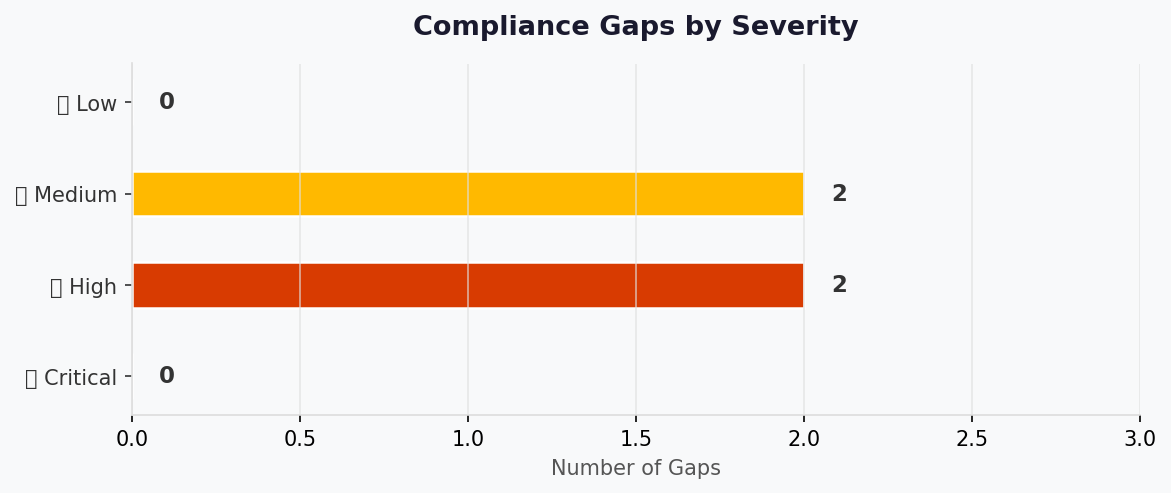
Design Document
Section titled “Design Document”- 📝 1. Introduction
- 🏛️ 2. Azure Architecture Overview
- 🌐 3. Networking
- 💾 4. Storage
- 💻 5. Compute
- 👤 6. Identity & Access
- 🔐 7. Security & Compliance
- 🔄 8. Backup & Disaster Recovery
- 📊 9. Management & Monitoring
- 📎 10. Appendix
- References
Generated by 08-As-Built agent | 2026-03-11
| ⬅️ Previous | 📑 Index | Next ➡️ |
|---|---|---|
| Design Document | Demo Index | Operations Runbook |
Version: 1.0 Date: 2026-03-11 Author: Generated by Workload Documentation Generator Status: Complete
📝 1. Introduction
Section titled “📝 1. Introduction”1.1 Document Purpose
Section titled “1.1 Document Purpose”This as-built design document captures the actual Azure deployment state for the FreshConnect MVP workload after successful Step 6 deployment.
Intended Audience:
- Solution Architects
- Operations/SRE Teams
- Security & Compliance Teams
- Development Teams
1.2 Project Overview
Section titled “1.2 Project Overview”Cloud-based farm-to-table ordering platform connecting farms, restaurants, and consumers across Scandinavia. Deployed as a cost-optimized N-tier web application in swedencentral with private data access paths for SQL, Storage, and Key Vault.
Business Objectives:
- Reduce order errors to below 1%
- Enable near-real-time order and inventory processing
- Maintain GDPR and PCI-DSS aligned security controls under startup budget
1.3 Design Objectives
Section titled “1.3 Design Objectives”| Objective | Target | Implementation |
|---|---|---|
| Availability | 99.9% | App Service Standard S1 with autoscale min 2, max 3 |
| Performance | p95 API < 500 ms | Co-located App Service + SQL in Sweden Central, S0 SQL baseline |
| Security | Private data paths, no secret sprawl | Key Vault + Managed Identity + private endpoints + public network disabled on data services |
| Scalability | 3x seasonal traffic | CPU autoscale policy 70% up / 30% down |
1.4 Constraints & Assumptions
Section titled “1.4 Constraints & Assumptions”Constraints:
- Budget ceiling around EUR 1,000/month
- EU data residency and policy-enforced tagging
Assumptions:
- Workload remains single-region for MVP
- Payment provider remains tokenized/redirect model (no CHD in Azure estate)
1.5 Stakeholders
Section titled “1.5 Stakeholders”| Role | Team | Responsibility |
|---|---|---|
| Platform Owner | Nordic Fresh Foods Engineering | Product and platform ownership |
| Operations | InfraOps / SRE | Runtime operations and incident response |
| Security & Compliance | Governance + Security | PCI/GDPR control evidence and remediation |
🏛️ 2. Azure Architecture Overview
Section titled “🏛️ 2. Azure Architecture Overview”2.1 Architecture Diagram
Section titled “2.1 Architecture Diagram”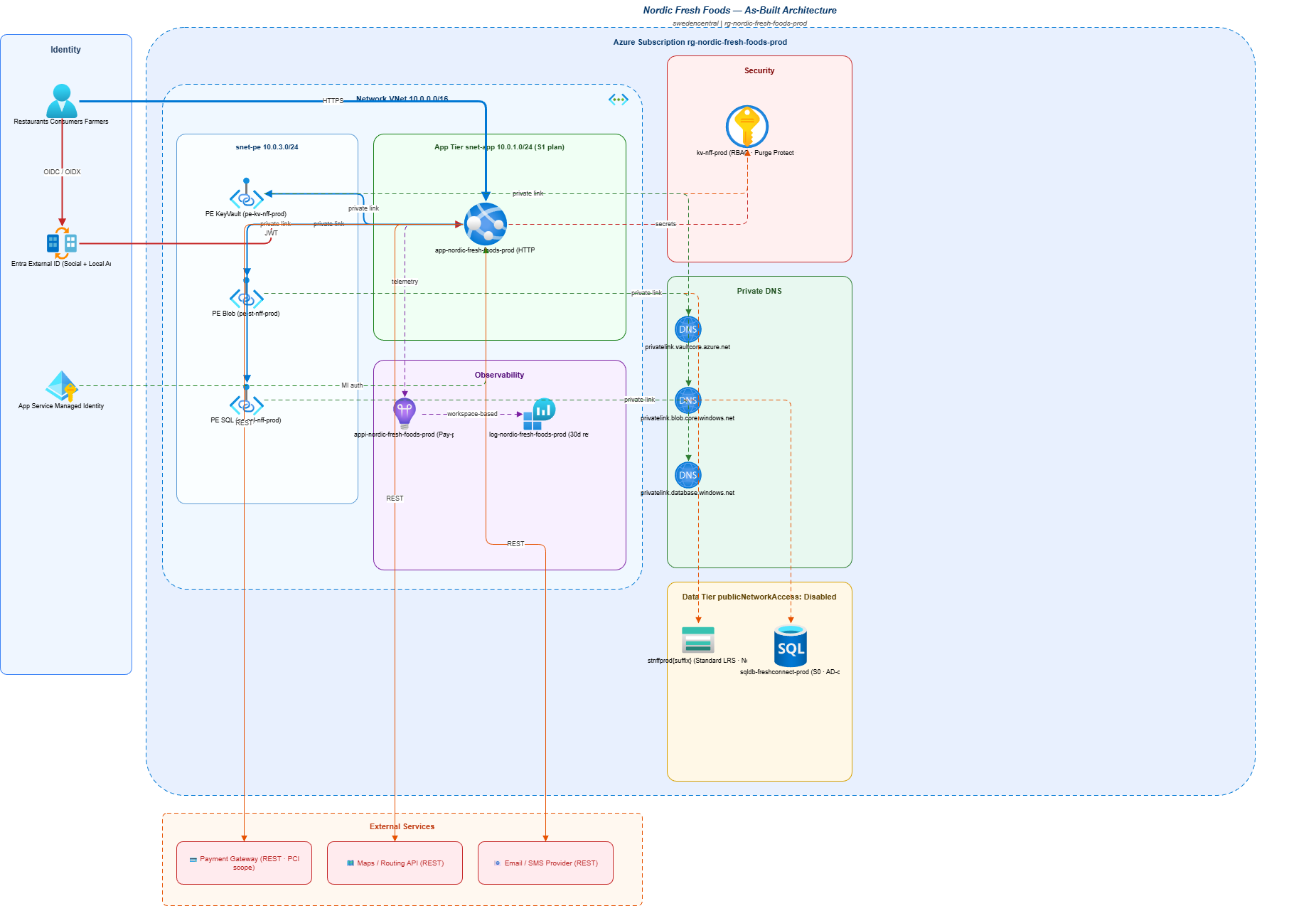
Source: As-built architecture Excalidraw source
2.2 Resource Summary
Section titled “2.2 Resource Summary”| Category | Count |
|---|---|
| Compute | 3 |
| Networking | 13 |
| Data | 6 |
| Security | 1 |
🌐 3. Networking
Section titled “🌐 3. Networking”The workload uses a single VNet (10.0.0.0/16) with 3 subnets:
snet-app(10.0.1.0/24) delegated toMicrosoft.Web/serverFarmssnet-data(10.0.2.0/24) reserved for data tiersnet-pe(10.0.3.0/24) for private endpoints (SQL, Blob, Key Vault)
Private DNS zones are linked to the VNet:
privatelink.database.windows.netprivatelink.blob.core.windows.netprivatelink.vaultcore.azure.net
Public network access is disabled for SQL Server, Storage Account, and Key Vault. App Service remains public (azurewebsites.net) with HTTPS-only.
💾 4. Storage
Section titled “💾 4. Storage”Storage account stnffprod7jrcjfo3iqckk is deployed as StorageV2 with Standard_LRS.
Key configuration:
enableHttpsTrafficOnly: trueminimumTlsVersion: TLS1_2allowBlobPublicAccess: falseallowSharedKeyAccess: falsepublicNetworkAccess: Disabled- Network default action:
Deny
Blob containers listed in deployment summary: assets, product-images.
💻 5. Compute
Section titled “💻 5. Compute”Compute tier consists of:
- App Service Plan
asp-nordic-fresh-foods-prod(Linux S1, capacity 2) - Web App
app-nordic-fresh-foods-prod-7jrcjf(state: Running) - Autoscale
autoscale-asp-nordic-fresh-foods-prod(2-3 instances)
Operational compute settings observed:
httpsOnly: trueftpsState: DisabledminTlsVersion: 1.2- System-assigned managed identity enabled
- VNet integration to
snet-app
👤 6. Identity & Access
Section titled “👤 6. Identity & Access”Identity model:
- User identity: Microsoft Entra External ID (application-level auth)
- Workload identity: System-assigned managed identity on App Service
- SQL admin: Entra group (
nordic-foods-dba), Azure AD-only authentication enabled
RBAC evidence:
- App Service managed identity granted
Key Vault Secrets Useron Key Vault scope.
🔐 7. Security & Compliance
Section titled “🔐 7. Security & Compliance”| Control | Implementation | Evidence |
|---|---|---|
| TLS 1.2+ | SQL min TLS 1.2, Storage TLS 1.2, Web App TLS 1.2 | az sql server show, az storage account show, az webapp show |
| HTTPS-only | Web App + Storage | httpsOnly: true, enableHttpsTrafficOnly: true |
| Managed Identity | App Service system-assigned identity | App Service principal ID 24cd6768-7247-43ac-a1d2-9a7f22000a40 |
| Network isolation | SQL/Storage/KV public access disabled + private endpoints | 3 private endpoints + 3 private DNS zones |
| Framework | Control ID | Status |
|---|---|---|
| GDPR | Data residency + access controls | ✅ |
| PCI-DSS v4 | Segmentation + encryption in transit | ✅ |
| Azure Policy | Required tags + SQL AAD-only auth | ✅ |
Open compliance risks:
- ⚠️ Several policy tags (
application,costcenter,backup-policy,maint-window,sla,workload) are present but empty values in deployed tags. - ❌ App Service ingress restrictions are currently allow-all (no WAF/IP restrictions configured).
🔄 8. Backup & Disaster Recovery
Section titled “🔄 8. Backup & Disaster Recovery”Current protection posture:
- SQL Database S0 with PITR (local backup redundancy)
- Key Vault soft delete (90 days) and purge protection enabled
- IaC reconstruction path available from
infra/bicep/nordic-fresh-foods/
MVP DR design remains single-region with documented failover strategy to germanywestcentral as manual recovery pattern.
📊 9. Management & Monitoring
Section titled “📊 9. Management & Monitoring”Monitoring stack:
- Log Analytics workspace
log-nordic-fresh-foods-prod(PerGB2018, 30-day retention, 2 GB/day cap) - Application Insights
appi-nordic-fresh-foods-prod(workspace-based, 50% sampling) - Autoscale policy on App Service Plan
- Resource group budget
budget-nordic-fresh-foods-prodwith actual+forecast notifications
📎 10. Appendix
Section titled “📎 10. Appendix”- Subscription:
00858ffc-dded-4f0f-8bbf-e17fff0d47d9 - Resource group:
rg-nordic-fresh-foods-prod - Region:
swedencentral - App endpoint:
https://app-nordic-fresh-foods-prod-7jrcjf.azurewebsites.net - SQL FQDN:
sql-nordic-fresh-foods-prod.database.windows.net - Key Vault URI:
https://kv-nff-prod-7jrcjfo3iqck.vault.azure.net/ - Storage blob endpoint:
https://stnffprod7jrcjfo3iqckk.blob.core.windows.net/
| Architecture | Link |
|---|---|
| Design-time architecture assessment | Architecture Assessment |
| Deployment outcomes | Deployment Summary |
References
Section titled “References”[!NOTE] 📚 The following Microsoft Learn resources provide additional guidance.
| Topic | Link |
|---|---|
| Well-Architected Framework | Overview |
| Azure Architecture Center | Architectures |
| Security Best Practices | Security Baseline |
| Networking Best Practices | Network Security |
| Backup Best Practices | Azure Backup |
| Monitoring Overview | Azure Monitor |
Design document generated from deployed infrastructure artifacts.
Operations Runbook
Section titled “Operations Runbook”- ⚡ Quick Reference
- 📋 1. Daily Operations
- 🚨 2. Incident Response
- 🔧 3. Common Procedures
- 🕐 4. Maintenance Windows
- 📞 5. Contacts & Escalation
- 📝 6. Change Log
- References
Generated by 08-As-Built agent | 2026-03-11
| ⬅️ Previous | 📑 Index | Next ➡️ |
|---|---|---|
| Design Document | Demo Index | Resource Inventory |
Version: 1.0 Date: 2026-03-11 Environment: prod Region: swedencentral
⚡ Quick Reference
Section titled “⚡ Quick Reference”| Item | Value |
|---|---|
| Primary Region | swedencentral |
| Resource Group | rg-nordic-fresh-foods-prod |
| Support Contact | technical-contact tag: sam@altman.com |
| Escalation Path | L1 On-call -> L2 Team Lead -> L3 Service Owner |
Critical Resources
Section titled “Critical Resources”| Resource | Name | Resource Group | Severity |
|---|---|---|---|
| App Service | app-nordic-fresh-foods-prod-7jrcjf | rg-nordic-fresh-foods-prod | 🔴 P1 |
| SQL Database | sqldb-freshconnect-prod | rg-nordic-fresh-foods-prod | 🔴 P1 |
| Key Vault | kv-nff-prod-7jrcjfo3iqck | rg-nordic-fresh-foods-prod | 🔴 P1 |
| Storage Account | stnffprod7jrcjfo3iqckk | rg-nordic-fresh-foods-prod | 🟠 P2 |
| Log Analytics | log-nordic-fresh-foods-prod | rg-nordic-fresh-foods-prod | 🟢 P3 |
📋 1. Daily Operations
Section titled “📋 1. Daily Operations”1.1 Health Checks
Section titled “1.1 Health Checks”Morning Health Check:
- ✅ Verify App Service is
Runningand responding on default hostname. - ✅ Verify SQL server state is
Readyand database isOnline. - ✅ Verify Key Vault/Storage/SQL private endpoints remain
Approved.
KQL Query - System Health Overview:
AppRequests| where TimeGenerated > ago(1h)| summarize Requests=count(), Failed=countif(Success == false), P95=percentile(DurationMs, 95)1.2 Log Review
Section titled “1.2 Log Review”Priority Logs to Review:
| Log Source | Query Focus | Action Threshold |
|---|---|---|
| Application Insights | Failed requests, dependency failures | >2% failures over 15 min |
| Log Analytics | Platform warnings/errors | Any Critical/Sev0 event |
| SQL diagnostics | Connection/auth anomalies | Repeated auth/network failures |
🚨 2. Incident Response
Section titled “🚨 2. Incident Response”2.1 Severity Definitions
Section titled “2.1 Severity Definitions”| Severity | Definition | Response Time |
|---|---|---|
| 🔴 P1 | Customer-impacting outage or data-path failure | 15 minutes |
| 🟠 P2 | Major feature degradation with workaround | 1 hour |
| 🟢 P3 | Non-critical issue or maintenance defect | 1 business day |
Incident Response Flow
Section titled “Incident Response Flow”flowchart LR
D["🔍 Detect"] --> T["🎯 Triage"]
T --> E["⚠️ Escalate"]
E --> R["🛠️ Resolve"]
R --> P["📝 Postmortem"]
style D fill:#D83B01,color:#fff
style R fill:#107C10,color:#fff
2.2 Runbooks by Alert
Section titled “2.2 Runbooks by Alert”| Alert | Runbook | Owner |
|---|---|---|
| App service unavailable | Restart app, inspect platform logs, validate VNet integration | App operations |
| SQL connectivity failures | Validate PE/DNS, test SQL endpoint, review auth | Data operations |
| Secret resolution failures | Check MI role assignment and Key Vault endpoint/health | Security operations |
| Budget threshold breach | Review cost drivers and scale settings | Platform owner |
🔧 3. Common Procedures
Section titled “🔧 3. Common Procedures”3.1 Restart Services
Section titled “3.1 Restart Services”az webapp restart \ --resource-group rg-nordic-fresh-foods-prod \ --name app-nordic-fresh-foods-prod-7jrcjf3.2 Scale Resources
Section titled “3.2 Scale Resources”# Manual override scale to 3 workersaz appservice plan update \ --resource-group rg-nordic-fresh-foods-prod \ --name asp-nordic-fresh-foods-prod \ --number-of-workers 3🕐 4. Maintenance Windows
Section titled “🕐 4. Maintenance Windows”| Task | Schedule | Duration |
|---|---|---|
| Platform patch + app updates | Sunday 02:00-06:00 UTC | 2-4 hours |
| DR and restore validation | Quarterly | 1 day |
gantt
title Maintenance Schedule
dateFormat YYYY-MM-DD
section Patching
OS Patching :a1, 2026-04-06, 1d
App Updates :a2, 2026-05-04, 1d
section DR Testing
Failover Test :b1, 2026-06-15, 1d
[!TIP] 💡 Apply changes during low-order windows and preserve rollback plan for SQL schema or config updates.
📞 5. Contacts & Escalation
Section titled “📞 5. Contacts & Escalation”| Role | Contact | Phone | On-Call Rotation |
|---|---|---|---|
| L1 On-call Engineer | Platform on-call | N/A | Weekly |
| L2 Team Lead | Engineering lead | N/A | Weekly |
| L3 Service Owner | Product/platform owner | N/A | Monthly |
Escalation Path
Section titled “Escalation Path”flowchart LR
L1["🟢 L1: On-Call Engineer"] --> L2["🟠 L2: Team Lead"]
L2 --> L3["🔴 L3: Service Owner"]
L3 --> MGMT["⚠️ Management"]
📝 6. Change Log
Section titled “📝 6. Change Log”| Date | Change | Author |
|---|---|---|
| 2026-03-11 | Initial as-built operations runbook created from deployed state | 08-As-Built agent |
References
Section titled “References”[!NOTE] 📚 The following Microsoft Learn resources provide operational guidance.
| Topic | Link |
|---|---|
| Azure Monitor Alerts | Alerting Best Practices |
| Log Analytics Queries | KQL Reference |
| Incident Management | Azure Status |
| Service Health | Azure Service Health |
Operations runbook generated from infrastructure artifacts.
Backup & DR Plan
Section titled “Backup & DR Plan”- 📋 Executive Summary
- 🎯 1. Recovery Objectives
- 💾 2. Backup Strategy
- 🌍 3. Disaster Recovery Procedures
- 🧪 4. Testing Schedule
- 📢 5. Communication Plan
- 👥 6. Roles and Responsibilities
- 🔗 7. Dependencies
- 📖 8. Recovery Runbooks
- 📎 9. Appendix
- References
Generated by 08-As-Built agent | 2026-03-11
| ⬅️ Previous | 📑 Index | Next ➡️ |
|---|---|---|
| Resource Inventory | Demo Index | Compliance Matrix |
Generated: 2026-03-11 Version: 1.0 Environment: prod Primary Region: swedencentral Secondary Region: germanywestcentral (planned failover target)
📋 Executive Summary
Section titled “📋 Executive Summary”[!IMPORTANT] This document defines the backup strategy and disaster recovery procedures for nordic-fresh-foods.
| Metric | Current | Target |
|---|---|---|
| RPO | SQL: service-managed PITR window; app data: daily operational backup pattern | 12 hours |
| RTO | Manual failover + redeploy strategy | 24 hours |
| Availability | Single-region with autoscale | 99.9% |
🎯 1. Recovery Objectives
Section titled “🎯 1. Recovery Objectives”1.1 Recovery Time Objective (RTO)
Section titled “1.1 Recovery Time Objective (RTO)”| Tier | RTO Target | Services |
|---|---|---|
| 🔴 Critical | 4-8 hours | App Service, SQL database, Key Vault |
| 🟠 Important | 8-16 hours | Storage assets, DNS private resolution |
| 🟢 Standard | 24 hours | Monitoring, non-critical integrations |
1.2 Recovery Point Objective (RPO)
Section titled “1.2 Recovery Point Objective (RPO)”| Data Type | RPO Target | Backup Strategy |
|---|---|---|
| Transactional data (SQL) | <= 12 hours | SQL automated backups + PITR |
| Blob assets | <= 24 hours | Export/snapshot operational process |
| Secrets/config | <= 24 hours | Key Vault recoverable soft-delete + IaC rehydration |
gantt
title RPO / RTO Targets by Tier
dateFormat HH:mm
axisFormat %H:%M
section Critical
RPO :crit, rpo1, 00:00, 12h
RTO :crit, rto1, 00:00, 8h
section Important
RPO :rpo2, 00:00, 24h
RTO :rto2, 00:00, 16h
section Standard
RPO :rpo3, 00:00, 24h
RTO :rto3, 00:00, 24h
💾 2. Backup Strategy
Section titled “💾 2. Backup Strategy”| Setting | Configuration |
|---|---|
| Backup Type | Platform-managed automated backups |
| Retention (PITR) | Service default for S0 tier |
| Long-Term Retention | Not configured in current deployment |
| Geo-Redundancy | Not enabled (local backup redundancy) |
Point-in-Time Restore Command:
az sql db restore \ --resource-group rg-nordic-fresh-foods-prod \ --server sql-nordic-fresh-foods-prod \ --name sqldb-freshconnect-prod \ --dest-name sqldb-freshconnect-prod-restored \ --time "2026-03-11T17:00:00Z"| Setting | Configuration |
|---|---|
| Soft Delete | Enabled |
| Purge Protection | Enabled |
🌍 3. Disaster Recovery Procedures
Section titled “🌍 3. Disaster Recovery Procedures”3.1 Failover Procedure
Section titled “3.1 Failover Procedure”- Confirm incident severity and regional impact in Azure Service Health.
- Restore SQL database to failover region (manual geo-restore or latest available backup path).
- Re-deploy stack from
infra/bicep/nordic-fresh-foods/with failover region parameters. - Rehydrate Key Vault secrets and validate managed identity permissions.
- Update DNS/app endpoint routing to failover deployment.
- Execute smoke tests and release service.
3.2 Failback Procedure
Section titled “3.2 Failback Procedure”- Validate primary region recovery.
- Synchronize latest data back to primary environment.
- Re-deploy primary resources from IaC.
- Switch traffic back during approved maintenance window.
- Run post-failback validation and close incident.
🧪 4. Testing Schedule
Section titled “🧪 4. Testing Schedule”| Test Type | Frequency | Last Test | Next Test |
|---|---|---|---|
| SQL PITR restore test | Quarterly | Not recorded | 2026-Q2 |
| Private endpoint + DNS validation | Quarterly | Not recorded | 2026-Q2 |
| Full tabletop DR exercise | Semi-annual | Not recorded | 2026-Q3 |
gantt
title DR Testing Schedule
dateFormat YYYY-MM-DD
section Backup Validation
SQL restore validation :a1, 2026-04-15, 1d
section Failover
Region failover drill :b1, 2026-06-15, 1d
section Full DR
Full DR exercise :c1, 2026-09-15, 2d
📢 5. Communication Plan
Section titled “📢 5. Communication Plan”| Audience | Channel | Template |
|---|---|---|
| Engineering on-call | Teams + Pager | P1/P2 incident template |
| Product stakeholders | Teams + Email | Service disruption notice |
| Compliance contacts | Security/compliance incident template |
👥 6. Roles and Responsibilities
Section titled “👥 6. Roles and Responsibilities”| Role | Team | Responsibility |
|---|---|---|
| Incident Commander | SRE lead | Owns incident bridge, decisions, and communications |
| Database Recovery Lead | Data platform | Executes SQL restore/failover tasks |
| Application Recovery Lead | App engineering | Re-deploys and validates application tier |
| Security Lead | Security/compliance | Verifies IAM, key access, and audit integrity |
🔗 7. Dependencies
Section titled “🔗 7. Dependencies”| Dependency | Impact | Mitigation |
|---|---|---|
| Azure SQL restore availability | Critical path for transactional recovery | Pre-tested restore runbooks and periodic drills |
| Private DNS resolution | App-to-data connectivity | Validate DNS links in every DR test |
| External payment/maps/email APIs | Functional degradation if unavailable | Circuit breaker + degraded mode behavior |
📖 8. Recovery Runbooks
Section titled “📖 8. Recovery Runbooks”| Scenario | Runbook | Owner |
|---|---|---|
| SQL data corruption | SQL PITR and app rebind | Database Recovery Lead |
| Region outage | Secondary region redeploy + traffic switch | Incident Commander |
| Secret compromise | Key rotation + app restart + audit | Security Lead |
Trigger: Data corruption or accidental destructive write. Estimated Duration: 1-3 hours.
- Identify last known good restore point.
- Run
az sql db restoreto a new database name. - Validate schema/data and update application connection reference.
- Restart app and run transactional smoke tests.
Validation:
az sql db show \ --resource-group rg-nordic-fresh-foods-prod \ --server sql-nordic-fresh-foods-prod \ --name sqldb-freshconnect-prod📎 9. Appendix
Section titled “📎 9. Appendix”- App hostname:
app-nordic-fresh-foods-prod-7jrcjf.azurewebsites.net - SQL FQDN:
sql-nordic-fresh-foods-prod.database.windows.net - Key Vault URI:
https://kv-nff-prod-7jrcjfo3iqck.vault.azure.net/ - Storage endpoint:
https://stnffprod7jrcjfo3iqckk.blob.core.windows.net/
References
Section titled “References”[!NOTE] 📚 The following Microsoft Learn resources provide DR guidance.
| Topic | Link |
|---|---|
| Azure Backup Overview | Backup Overview |
| Backup Best Practices | Best Practices |
| RTO/RPO Guidance | Reliability Metrics |
| Site Recovery | ASR Overview |
| Business Continuity | DR Planning |
Backup and DR plan generated from infrastructure artifacts.
Compliance Matrix
Section titled “Compliance Matrix”- 📋 Executive Summary
- 🗺️ 1. Control Mapping
- 🔍 2. Gap Analysis
- 📁 3. Evidence Collection
- 📝 4. Audit Trail
- 🔧 5. Remediation Tracker
- 📎 6. Appendix
- References
Generated by 08-As-Built agent | 2026-03-11
| ⬅️ Previous | 📑 Index | Next ➡️ |
|---|---|---|
| Backup & DR Plan | Demo Index | Cost Estimate |
Generated: 2026-03-11 Version: 1.0 Environment: prod Primary Compliance Framework: GDPR + PCI-DSS v4 + Azure Policy baseline
📋 Executive Summary
Section titled “📋 Executive Summary”[!IMPORTANT] This compliance matrix maps the nordic-fresh-foods security controls to GDPR and PCI-DSS-aligned requirements.
| Compliance Area | Coverage | Status |
|---|---|---|
| Network Security | 88% | ⚠️ |
| Data Protection | 94% | ✅ |
| Access Control | 90% | ✅ |
| Monitoring & Audit | 82% | ⚠️ |
| Incident Response | 78% | ⚠️ |
| Overall | 86% | ⚠️ |
🗺️ 1. Control Mapping
Section titled “🗺️ 1. Control Mapping”Requirement 1: Data protection and secure transport
Section titled “Requirement 1: Data protection and secure transport”| Control | Requirement | Implementation | Status |
|---|---|---|---|
| TLS enforcement | Encrypt data in transit | SQL min TLS 1.2, Storage TLS1_2, App Service TLS 1.2 | ✅ |
| Public exposure minimization | Restrict direct data service access | SQL/Storage/KV publicNetworkAccess: Disabled, private endpoints configured | ✅ |
| Secret handling | Centralized secret management and no hardcoded keys | Key Vault Premium + App Service managed identity + KV RBAC role assignment | ✅ |
Evidence Location: Azure CLI evidence captured during Step 7 generation.
| Evidence Item | Type | Date Collected |
|---|---|---|
az sql server show output | CLI JSON | 2026-03-11 |
az storage account show output | CLI JSON | 2026-03-11 |
az keyvault show output | CLI JSON | 2026-03-11 |
Requirement 2: Identity and least privilege
Section titled “Requirement 2: Identity and least privilege”| Control | Requirement | Implementation | Status |
|---|---|---|---|
| SQL AAD-only auth | No SQL local auth for admin | azureAdOnlyAuthentication: true on SQL server | ✅ |
| Workload identity | Service-to-service auth without shared secrets | App Service system-assigned managed identity | ✅ |
| Key Vault data-plane role | Least privilege secret access | Key Vault Secrets User scoped to vault | ✅ |
Evidence Location: Azure RBAC and SQL server properties.
| Evidence Item | Type | Date Collected |
|---|---|---|
az role assignment list --scope <kv-id> | CLI JSON | 2026-03-11 |
| SQL administrators block | CLI JSON | 2026-03-11 |
Requirement 3: Governance and policy compliance
Section titled “Requirement 3: Governance and policy compliance”| Control | Requirement | Implementation | Status |
|---|---|---|---|
| Mandatory tags | Policy-required tags populated | Required keys present but several values are empty | ⚠️ |
| Budget controls | Cost governance and notifications | RG monthly budget with actual/forecast thresholds | ✅ |
| Monitoring baseline | Centralized logs and telemetry | Log Analytics + Application Insights | ✅ |
Evidence Location: Resource tags, budget resource, monitoring resources.
| Evidence Item | Type | Date Collected |
|---|---|---|
az resource list tags snapshot | CLI JSON | 2026-03-11 |
az consumption budget list --resource-group | CLI JSON | 2026-03-11 |
| Workspace/component show outputs | CLI JSON | 2026-03-11 |
🔍 2. Gap Analysis
Section titled “🔍 2. Gap Analysis”| Gap | Severity | Risk Level | Remediation | Timeline |
|---|---|---|---|---|
Empty policy tag values (application, costcenter, sla, backup-policy, maint-window, workload) | 🟠 | Medium | Update Bicep parameters and redeploy tags | 2 weeks |
App Service ingress and SCM rules allow all (Allow all) | 🟠 | Medium | Add IP restrictions/WAF/Front Door controls | 4 weeks |
| Log Analytics public query/ingestion still enabled | 🟡 | Medium | Evaluate Private Link and disable public access as feasible | 4-6 weeks |
| DR test evidence not yet recorded | 🟡 | Low | Execute and capture quarterly restore/failover drills | 1 quarter |
| App Service lacks WAF/Front Door protection | 🟠 | High | ❌ Deploy WAF or Front Door before production traffic | Pre-prod |
📁 3. Evidence Collection
Section titled “📁 3. Evidence Collection”| Control | Evidence Type | Location | Last Collected |
|---|---|---|---|
| SQL AAD-only auth | CLI output | Step 7 command capture | 2026-03-11 |
| Storage hardened config | CLI output | Step 7 command capture | 2026-03-11 |
| Key Vault security baseline | CLI output | Step 7 command capture | 2026-03-11 |
| Autoscale and budget controls | CLI output | Step 7 command capture | 2026-03-11 |
| Private networking controls | CLI output | Step 7 command capture | 2026-03-11 |
📝 4. Audit Trail
Section titled “📝 4. Audit Trail”| Date | Auditor | Finding | Status | Commit |
|---|---|---|---|---|
| 2026-03-11 | 08-As-Built agent | As-built compliance evidence consolidated | Complete | N/A |
| 2026-03-11 | Deploy workflow | Phase 4 SQL configuration mismatch fixed (zoneRedundant: false) | Complete | N/A |
🔧 5. Remediation Tracker
Section titled “🔧 5. Remediation Tracker”| Finding | Owner | Due Date | Status |
|---|---|---|---|
| Populate all policy-required tag values | Platform engineering | 2026-03-25 | ⬜ Todo |
| Lock down App Service ingress/SCM rules | Security engineering | 2026-04-08 | ⬜ Todo |
| Assess and harden Log Analytics public access | Operations | 2026-04-15 | ⬜ Todo |
| Run and record DR drills | SRE lead | 2026-06-30 | ⬜ Todo |
📎 6. Appendix
Section titled “📎 6. Appendix”A. Compliance Framework Reference
Section titled “A. Compliance Framework Reference”- GDPR (EU data residency and data protection controls)
- PCI-DSS v4 (segmentation, encryption, access management)
- Azure Policy governance constraints from
04-governance-constraints.md
B. Azure Security Baseline Mapping
Section titled “B. Azure Security Baseline Mapping”- HTTPS-only and TLS 1.2 controls applied on web/data services
- Data services isolated via private endpoints and public network disablement
- Managed identity used for workload-to-secret access
- Centralized monitoring via Log Analytics + App Insights
References
Section titled “References”flowchart LR
A["Control"] --> B{"Implemented?"}
B -- Yes --> C{"Evidence Collected?"}
B -- No --> D["❌ Gap"]
C -- Yes --> E["✅ Compliant"]
C -- No --> F["⚠️ Pending Evidence"]
D --> G["Remediation Tracker"]
style E fill:#107C10,color:#fff
style D fill:#D83B01,color:#fff
style F fill:#FFB900,color:#000
[!NOTE] 📚 The following Microsoft Learn resources provide compliance guidance.
| Topic | Link |
|---|---|
| Microsoft Cloud Security Benchmark | MCSB Overview |
| Azure Compliance Offerings | Compliance |
| Azure Policy | Policy Overview |
| Regulatory Compliance | Built-in Policies |
Compliance matrix generated from infrastructure artifacts.
Resource Inventory
Section titled “Resource Inventory”Generated by 08-As-Built agent | 2026-03-11
| ⬅️ Previous | 📑 Index | Next ➡️ |
|---|---|---|
| Operations Runbook | Demo Index | Backup & DR Plan |
Generated: 2026-03-11 Source: Azure deployed state + Bicep artifacts Environment: prod Region: swedencentral
📊 Summary
Section titled “📊 Summary”| Category | Count |
|---|---|
| Total Resources | 24 |
| 💻 Compute | 3 |
| 💾 Data Services | 6 |
| 🌐 Networking | 13 |
| 📨 Messaging | 0 |
| 🔐 Security | 1 |
| 📊 Monitoring | 2 |
[!NOTE] Resource count includes governance/ops resources (budget and autoscale), private networking artifacts (private endpoints + NICs + private DNS zones), and SQL
mastersystem database.
📦 Resource Listing
Section titled “📦 Resource Listing”💻 Compute Resources
Section titled “💻 Compute Resources”| Name | Type | SKU | Location | Monthly Cost | Purpose | Portal |
|---|---|---|---|---|---|---|
| asp-nordic-fresh-foods-prod | Microsoft.Web/serverFarms | S1 (capacity 2) | swedencentral | $146.00 | Linux App Service Plan for web/API workload | View |
| app-nordic-fresh-foods-prod-7jrcjf | Microsoft.Web/sites | Standard (on S1 plan) | swedencentral | $0.00 (plan-backed) | FreshConnect application endpoint | View |
| autoscale-asp-nordic-fresh-foods-prod | Microsoft.Insights/autoscalesettings | N/A | swedencentral | $0.00 | Autoscale policy for App Service Plan (min 2, max 3) | View |
💾 Data Services
Section titled “💾 Data Services”| Name | Type | SKU | Configuration | Location | Monthly Cost |
|---|---|---|---|---|---|
| sql-nordic-fresh-foods-prod | Microsoft.Sql/servers | v12.0 | Azure AD-only auth, public network disabled, TLS 1.2 | swedencentral | $0.00 |
| sqldb-freshconnect-prod | Microsoft.Sql/servers/databases | S0 (Standard, 10 DTU) | Max size 250 GB, zoneRedundant false, status Online | swedencentral | $14.71 |
| master | Microsoft.Sql/servers/databases | System | System database | swedencentral | Included |
| stnffprod7jrcjfo3iqckk | Microsoft.Storage/storageAccounts | Standard_LRS | HTTPS-only, public network disabled, no shared key auth, no public blob access | swedencentral | $1.86 (assumed 50 GB hot + txns) |
| assets | Blob container | N/A | Documented in deployment summary; data-plane read blocked by network rules | swedencentral | Included |
| product-images | Blob container | N/A | Documented in deployment summary; data-plane read blocked by network rules | swedencentral | Included |
🌐 Networking Resources
Section titled “🌐 Networking Resources”| Name | Type | Configuration | Location |
|---|---|---|---|
| vnet-nordic-fresh-foods-prod | Microsoft.Network/virtualNetworks | 10.0.0.0/16 with snet-app (10.0.1.0/24), snet-data (10.0.2.0/24), snet-pe (10.0.3.0/24) | swedencentral |
| nsg-nordic-fresh-foods-app-prod | Microsoft.Network/networkSecurityGroups | NSG bound to snet-app | swedencentral |
| nsg-nordic-fresh-foods-data-prod | Microsoft.Network/networkSecurityGroups | NSG bound to snet-data | swedencentral |
| nsg-nordic-fresh-foods-pe-prod | Microsoft.Network/networkSecurityGroups | NSG bound to snet-pe | swedencentral |
| pep-sql-nordic-fresh-foods-prod-sqlServer-0 | Microsoft.Network/privateEndpoints | SQL private endpoint | swedencentral |
| pep-stnffprod7jrcjfo3iqckk-blob-0 | Microsoft.Network/privateEndpoints | Blob private endpoint | swedencentral |
| pep-kv-nff-prod-7jrcjfo3iqck-vault-0 | Microsoft.Network/privateEndpoints | Key Vault private endpoint | swedencentral |
| pep-sql-…nic… | Microsoft.Network/networkInterfaces | NIC for SQL PE | swedencentral |
| pep-st…nic… | Microsoft.Network/networkInterfaces | NIC for Blob PE | swedencentral |
| pep-kv-…nic… | Microsoft.Network/networkInterfaces | NIC for KV PE | swedencentral |
| privatelink.database.windows.net | Microsoft.Network/privateDnsZones | SQL private DNS zone with VNet link | global |
| privatelink.blob.core.windows.net | Microsoft.Network/privateDnsZones | Blob private DNS zone with VNet link | global |
| privatelink.vaultcore.azure.net | Microsoft.Network/privateDnsZones | Key Vault private DNS zone with VNet link | global |
📨 Messaging Resources
Section titled “📨 Messaging Resources”| Name | Type | SKU | Configuration | Location |
|---|---|---|---|---|
| None | N/A | N/A | Messaging services were not deployed in this workload | N/A |
🔐 Security Resources
Section titled “🔐 Security Resources”| Name | Type | Configuration | Location |
|---|---|---|---|
| kv-nff-prod-7jrcjfo3iqck | Microsoft.KeyVault/vaults | Premium, RBAC enabled, soft delete 90 days, purge protection enabled, public network disabled | swedencentral |
📊 Monitoring Resources
Section titled “📊 Monitoring Resources”| Name | Type | Retention | Location |
|---|---|---|---|
| log-nordic-fresh-foods-prod | Microsoft.OperationalInsights/workspaces | 30 days | swedencentral |
| appi-nordic-fresh-foods-prod | Microsoft.Insights/components | 365 days | swedencentral |
💰 Governance Resources
Section titled “💰 Governance Resources”| Name | Type | Configuration | Location |
|---|---|---|---|
| budget-nordic-fresh-foods-prod | Microsoft.Consumption/budgets | USD 800 monthly budget, actual 90% + forecast 80/100/120% notifications | rg scope |
pie showData
title Resource Distribution by Category
"💻 Compute" : 3
"💾 Data" : 6
"🌐 Networking" : 13
"📨 Messaging" : 0
"🔐 Security" : 1
"📊 Monitoring" : 2
References
Section titled “References”| Topic | Link |
|---|---|
| Azure Resource Types | Resource Providers |
| Naming Conventions | CAF Naming |
| Pricing Calculator | Azure Pricing |
Resource inventory generated from deployed resources and Bicep templates.
Cost Estimate
Section titled “Cost Estimate”- 💵 Cost At-a-Glance
- ✅ Decision Summary
- 🔁 Requirements → Cost Mapping
- 📊 Top 5 Cost Drivers
- 🏛️ Architecture Overview
- 🧾 What We Are Not Paying For (Yet)
- ⚠️ Cost Risk Indicators
- 🎯 Quick Decision Matrix
- 💰 Savings Opportunities
- 🧾 Detailed Cost Breakdown
- References
Generated by 08-As-Built agent | 2026-03-11
| ⬅️ Previous | 📑 Index | Next ➡️ |
|---|---|---|
| Compliance Matrix | Demo Index | — |
Generated: 2026-03-11
Source: Deployed resources + cost-estimate-subagent MCP pricing response
Region: swedencentral
Environment: Production
MCP Tools Used: azure_bulk_estimate, azure_cost_estimate, azure_price_search, azure_sku_discovery (via subagent)
IaC Reference: Bicep templates repository folder
💵 Cost At-a-Glance
Section titled “💵 Cost At-a-Glance”Monthly Total: $363.77 | Annual: $4,365.24
Status Indicator Cost Trend ➡️ Stable (monitoring-heavy profile) Savings Available 💰 Potential with monitoring ingestion tuning Compliance ✅ GDPR and PCI-DSS aligned controls deployed
✅ Decision Summary
Section titled “✅ Decision Summary”- ✅ Implemented: App Service S1 (2 instances), SQL S0, private endpoints (3), Key Vault Premium, Storage LRS, monitoring stack, budget alerts.
- ⏳ Deferred: WAF/Application Gateway, DDoS Standard, multi-region active-passive architecture.
- 🔁 Redesign Trigger: Sustained 3-instance runtime plus high telemetry ingestion pushes total toward budget threshold.
Confidence: Medium | Expected Variance: +/-20% (telemetry ingestion and unresolved PE meter are primary variables)
Design vs As-Built Summary
Section titled “Design vs As-Built Summary”| Metric | Design Estimate | As-Built | Variance | Status |
|---|---|---|---|---|
| Monthly Estimate | $203.97 | $363.77 | +$159.80 | ⚠️ |
| Annual Estimate | $2,447.64 | $4,365.24 | +$1,917.60 | ⚠️ |
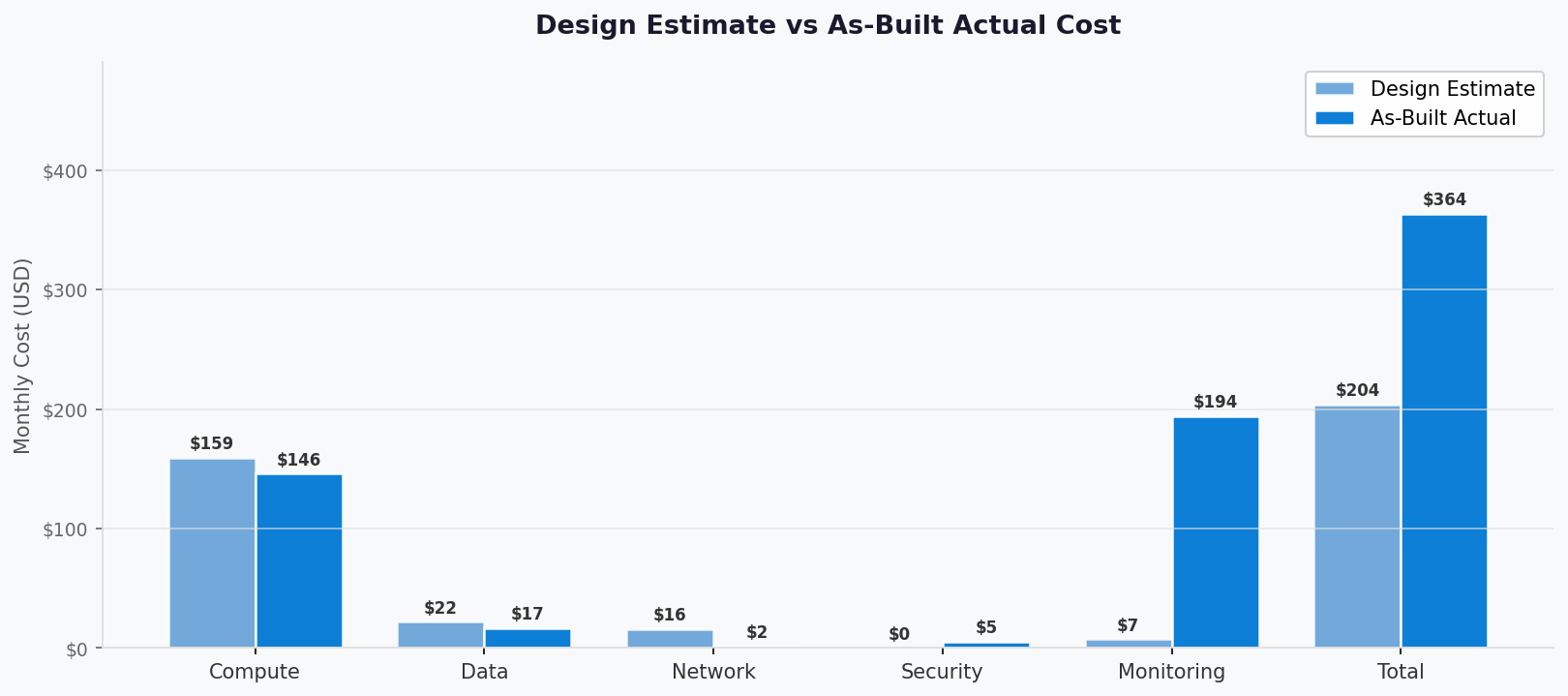
🔁 Requirements → Cost Mapping
Section titled “🔁 Requirements → Cost Mapping”| Requirement | Architecture Decision | Cost Impact | Mandatory |
|---|---|---|---|
| SLA 99.9% | S1 App Service with min 2 instances | +$146.00/month | Yes |
| GDPR/PCI network isolation | 3 Private Endpoints + 3 Private DNS zones | +$1.50/month in current priced output (PE unresolved) | Yes |
| Relational transaction store | SQL S0 single database | +$14.71/month | Yes |
| Observability baseline | Log Analytics + App Insights | +$194.40/month | Yes |
📊 Top 5 Cost Drivers
Section titled “📊 Top 5 Cost Drivers”| Rank | Resource | Monthly Cost | % of Total | Trend | Optimization |
|---|---|---|---|---|---|
| 1️⃣ | Log Analytics ingestion | $179.40 | 49.32% | ⬆️ | Reduce ingestion volume and noisy logs |
| 2️⃣ | App Service Plan S1 x2 | $146.00 | 40.13% | ➡️ | Validate sustained capacity requirement |
| 3️⃣ | Application Insights | $15.00 | 4.12% | ➡️ | Sampling/retention tuning |
| 4️⃣ | SQL Database S0 | $14.71 | 4.04% | ➡️ | Keep S0 until sustained pressure |
| 5️⃣ | Key Vault Premium | $5.30 | 1.46% | ➡️ | Right-size ops and vault SKU if allowable |
💡 Quick Win: Prioritize telemetry filtering and ingestion caps; this has the largest single cost-reduction potential.
1️⃣ Monitoring Stack
Section titled “1️⃣ Monitoring Stack”| Aspect | Detail |
|---|---|
| Current Inputs | Log Analytics estimated at 2 GB/day and App Insights workspace-based |
| Monthly Cost | $194.40 |
| Optimization | Refine data collection and reduce high-cardinality telemetry |
| Potential Savings | Significant, workload-dependent |
🏛️ Architecture Overview
Section titled “🏛️ Architecture Overview”Cost Distribution
Section titled “Cost Distribution”| Category | Monthly Cost (USD) | Share |
|---|---|---|
| 💻 Compute | 146.00 | 40.13% |
| 💾 Data Services | 16.57 | 4.56% |
| 🌐 Networking | 1.50 | 0.41% |
| 🔐 Security | 5.30 | 1.46% |
| 📊 Monitoring | 194.40 | 53.45% |
| Other | 0.00 | 0.00% |
Month-over-Month Projection
Section titled “Month-over-Month Projection”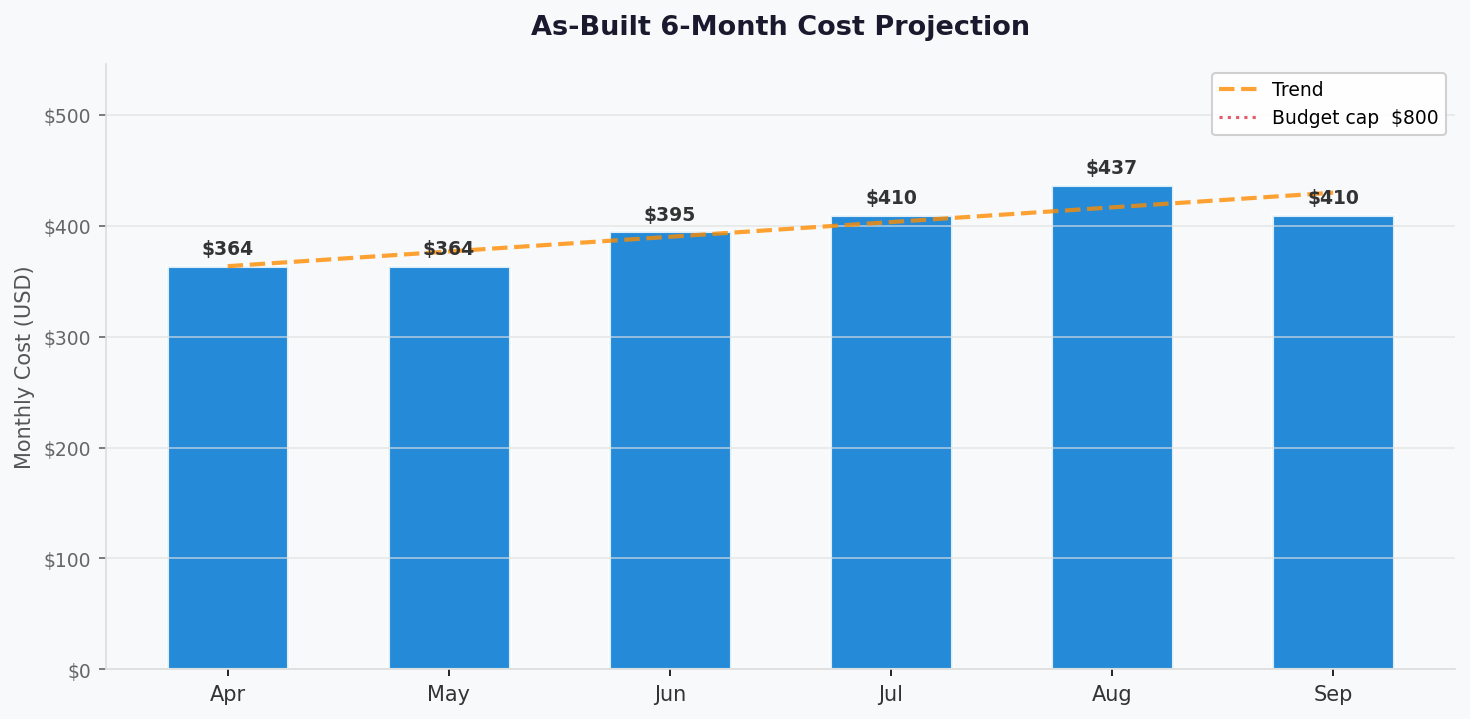
Key Design Decisions Affecting Cost
Section titled “Key Design Decisions Affecting Cost”| Decision | Cost Impact | Business Rationale | Status |
|---|---|---|---|
| Min 2 App Service instances | +$146.00/month | Availability and peak readiness | Required |
| Telemetry cap + workspace monitor | +$194.40/month in current estimate | Operational visibility | Required |
| SQL S0 baseline | +$14.71/month | MVP transactional requirements | Required |
🧾 What We Are Not Paying For (Yet)
Section titled “🧾 What We Are Not Paying For (Yet)”- Azure WAF/Application Gateway v2
- Azure DDoS Protection Standard
- Multi-region active-passive duplicate stack
- Redis cache tier
⚠️ Cost Risk Indicators
Section titled “⚠️ Cost Risk Indicators”| Resource | Risk Level | Issue | Mitigation |
|---|---|---|---|
| Log Analytics | 🔴 High | Ingestion estimate dominates monthly spend | Reduce ingestion and tune diagnostic categories |
| Private Endpoints | 🟡 Medium | Region meter unresolved in pricing tool | Re-check meter mapping in next cost cycle |
| App Service Plan | 🟡 Medium | Scale-to-3 scenarios increase compute by $73.00 | Track autoscale events and seasonal run rate |
⚠️ Watch Item: Monitoring assumptions currently drive the delta versus design estimate.
🎯 Quick Decision Matrix
Section titled “🎯 Quick Decision Matrix”“If you need X, expect to pay Y more”
| Requirement | Additional Cost | SKU Change | Verdict | Notes |
|---|---|---|---|---|
| Seasonal scale-to-3 | +$73.00/month | S1 instances 2 -> 3 | 🟢 Go | Included in autoscale profile |
| Full WAF tier | Not in current as-built | Add App Gateway WAF_v2 | 🟡 Monitor | Evaluate post-MVP |
| Multi-region DR | Not in current as-built | Duplicate stack in failover region | ❌ Budget impact material | Evaluate post-MVP |
💰 Savings Opportunities
Section titled “💰 Savings Opportunities”Total Potential Savings: Variable (telemetry and retention tuning dependent)
Section titled “Total Potential Savings: Variable (telemetry and retention tuning dependent)”
Strategy Commitment Monthly Savings Annual Savings % Reduction Log filtering + category tuning N/A Variable Variable Variable App Insights ingestion tuning N/A Variable Variable Variable Planned peak-window scaling only N/A Up to $73 in non-peak periods Up to $876 20.07%
🧾 Detailed Cost Breakdown
Section titled “🧾 Detailed Cost Breakdown”IaC / Pricing Coverage
Section titled “IaC / Pricing Coverage”| Signal | Value | Status |
|---|---|---|
| Templates scanned | 9 Bicep files | ✅ |
| Resources detected | 24 as-built resources | ✅ |
| Resources priced | 10 primary billable meters | ✅ |
| Unpriced resources | Private Endpoint meter unresolved in tool output | ⚠️ |
Line Items
Section titled “Line Items”| Category | Service | SKU / Meter | Quantity / Units | Est. Monthly |
|---|---|---|---|---|
| 💻 Compute | App Service Plan | S1 Linux | 2 instances x 730h | $146.00 |
| 💻 Compute | App Service Site | Plan-backed | 1 | $0.00 |
| 💾 Data Services | Azure SQL DB | S0 | 1 database | $14.71 |
| 💾 Data Services | Storage (Hot LRS + txns) | Blob + transactions | 50 GB + 100K txns | $1.86 |
| 🔐 Security | Key Vault Premium | Base + ops | 1 vault + 100K ops | $5.30 |
| 🌐 Networking | Private DNS Zones | Private DNS | 3 zones | $1.50 |
| 🌐 Networking | Private Endpoints | PE meter | 3 endpoints | $0.00 (unresolved) |
| 📊 Monitoring | Log Analytics | Analytics Logs | 2 GB/day (~60 GB/mo) | $179.40 |
| 📊 Monitoring | Application Insights | Enterprise meter | 1 component | $15.00 |
| Other | Budget, NSGs, VNet, NICs, autoscale | N/A | N/A | $0.00 |
- All dollar figures above are from
cost-estimate-subagentoutput and were not manually adjusted. - The Private Endpoint meter did not resolve for
swedencentralin the subagent output. - Design estimate from Step 3 used lower monitoring assumptions, causing the main variance.
References
Section titled “References”| Topic | Link |
|---|---|
| Azure Pricing Calculator | Calculator |
| Cost Management | Overview |
| Reserved Instances | Reservations |
| WAF Cost Optimization | Checklist |
| ⬅️ Compliance Matrix | 🏠 Demo Index | ➡️ — |
|---|