Not every resource deploys in every scenario. The SCENARIO parameter controls which optional components are included:
- NAT Gateway: Deployed when there is no Azure Firewall (baseline, vpn). When Firewall is present, it handles outbound traffic.
- Azure Firewall + Route Tables: Deployed in firewall and full scenarios. Route tables force all spoke traffic through the Firewall via UDR.
- VPN Gateway: Deployed in vpn and full scenarios. Requires
ON_PREMISES_ADDRESS_SPACE parameter.
- VNet Peering: Created whenever Firewall or VPN Gateway is deployed (firewall, vpn, full). Baseline has no peering — hub and spoke are independent.
| Resource | Type | RG | baseline | firewall | vpn | full |
|---|
vnet-hub-smb-{r} | Virtual Network | hub | ✅ | ✅ | ✅ | ✅ |
nsg-hub-smb-{r} | Network Security Group | hub | ✅ | ✅ | ✅ | ✅ |
pdnsz-* | Private DNS Zone | hub | ✅ | ✅ | ✅ | ✅ |
fw-hub-smb-{r} | Azure Firewall | hub | — | ✅ | — | ✅ |
fwpol-hub-smb-{r} | Firewall Policy | hub | — | ✅ | — | ✅ |
pip-fw-hub-smb-{r} | Public IP (FW) | hub | — | ✅ | — | ✅ |
pip-fw-mgmt-hub-smb-{r} | Public IP (FW Mgmt) | hub | — | ✅ | — | ✅ |
vpng-hub-smb-{r} | VPN Gateway | hub | — | — | ✅ | ✅ |
pip-vpng-hub-smb-{r} | Public IP (VPN) | hub | — | — | ✅ | ✅ |
rt-spoke-smb-{r} | Route Table (spoke) | hub | — | ✅ | — | ✅ |
rt-gateway-smb-{r} | Route Table (gateway) | hub | — | ✅ | — | ✅ |
vnet-spoke-prod-{r} | Virtual Network | spoke | ✅ | ✅ | ✅ | ✅ |
nsg-spoke-prod-{r} | Network Security Group | spoke | ✅ | ✅ | ✅ | ✅ |
nat-spoke-prod-{r} | NAT Gateway | spoke | ✅ | — | ✅ | — |
pip-nat-prod-{r} | Public IP (NAT) | spoke | ✅ | — | ✅ | — |
log-smbrf-smb-{r} | Log Analytics Workspace | monitor | ✅ | ✅ | ✅ | ✅ |
aa-smbrf-smb-{r} | Automation Account | monitor | ✅ | ✅ | ✅ | ✅ |
rsv-smbrf-smb-{r} | Recovery Services Vault | backup | ✅ | ✅ | ✅ | ✅ |
kv-smbrf-{r}-{suffix} | Key Vault | security | ✅ | ✅ | ✅ | ✅ |
pep-kv-smbrf-smb-{r} | Private Endpoint | security | ✅ | ✅ | ✅ | ✅ |
migrate-smbrf-smb-{r} | Azure Migrate Project | migrate | ✅ | ✅ | ✅ | ✅ |
{r} = region abbreviation (e.g., swc for swedencentral)
| Resource | Type | Scenarios |
|---|
budget-smb-monthly | Budget ($500) | All |
| Defender for Cloud | Security Pricing (Free) | All |
| Policy assignments | MG + subscription scoped | All |
| VNet Peering (hub↔spoke) | Network Peering | firewall, vpn, full |
| Subnet | Address Range | Purpose |
|---|
| AzureFirewallSubnet | 10.0.0.0/26 | Azure Firewall data plane |
| AzureFirewallManagementSubnet | 10.0.0.64/26 | Azure Firewall management |
| snet-management | 10.0.0.128/26 | Management VMs |
| GatewaySubnet | 10.0.0.192/27 | VPN Gateway |
| AzureBastionSubnet | 10.0.0.224/27 | Azure Bastion Developer |
| Subnet | Address Range | Purpose | UDR Applied |
|---|
| snet-workload | 10.0.2.0/25 | General workloads | ✅ (when FW) |
| snet-data | 10.0.2.128/25 | Database/storage | ✅ (when FW) |
| snet-app | 10.0.3.0/25 | Application tier | ✅ (when FW) |
| snet-pep | 10.0.3.128/26 | Private endpoints | — |
| # | AVM Module | Version | Used In |
|---|
| 1 | network/virtual-network | 0.8.0 | networking-hub, networking-spoke |
| 2 | network/network-security-group | 0.5.3 | networking-hub, networking-spoke |
| 3 | network/nat-gateway | 2.1.0 | networking-spoke |
| 4 | network/public-ip-address | 0.12.0 | firewall |
| 5 | network/azure-firewall | 0.10.1 | firewall |
| 6 | network/firewall-policy | 0.3.4 | firewall |
| 7 | network/route-table | 0.5.0 | route-tables |
| 8 | network/virtual-network-gateway | 0.10.1 | vpn-gateway |
| 9 | network/private-dns-zone | 0.8.1 | networking-hub, keyvault |
| 10 | key-vault/vault | 0.13.3 | keyvault |
| 11 | operational-insights/workspace | 0.15.0 | monitoring |
| 12 | automation/automation-account | 0.19.0 | automation |
| 13 | recovery-services/vault | 0.11.1 | backup |
The Terraform track uses raw azurerm_* / azapi_resource instead of AVM-TF registry modules. See ADR-0005 for rationale.
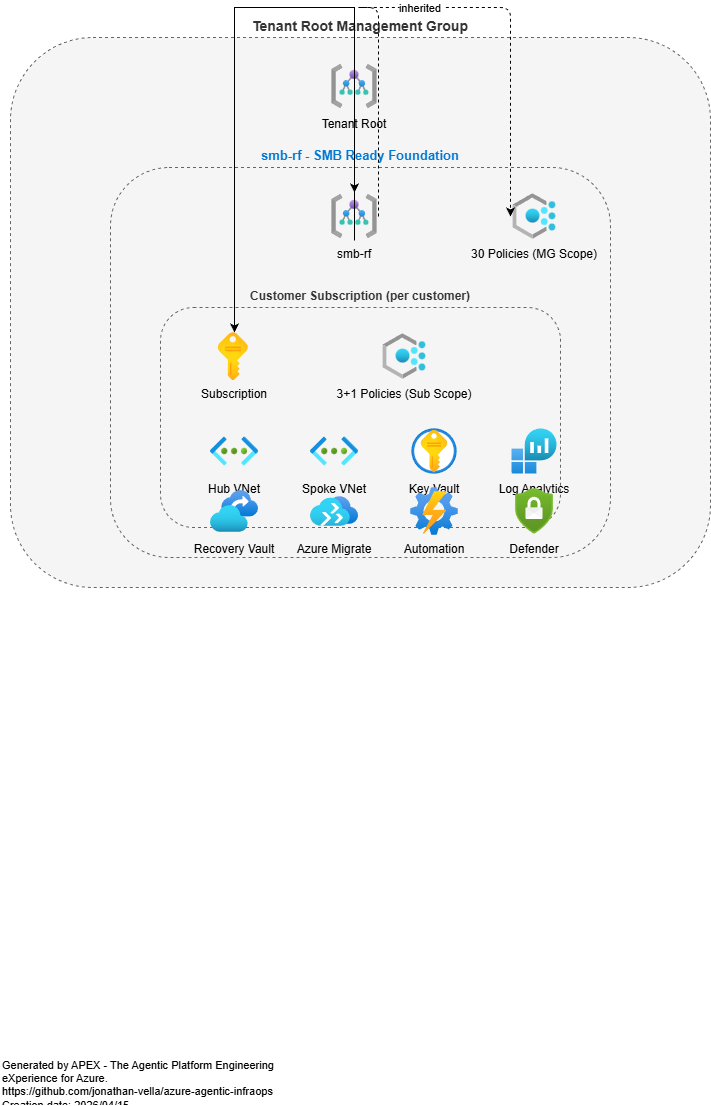
17 child modules: management-group, policy-assignments-mg, resource-groups, budget, defender, network-hub, network-spoke, firewall, route-tables, vpn-gateway, peering, monitoring, backup, policy-backup-auto, migrate, keyvault, automation.
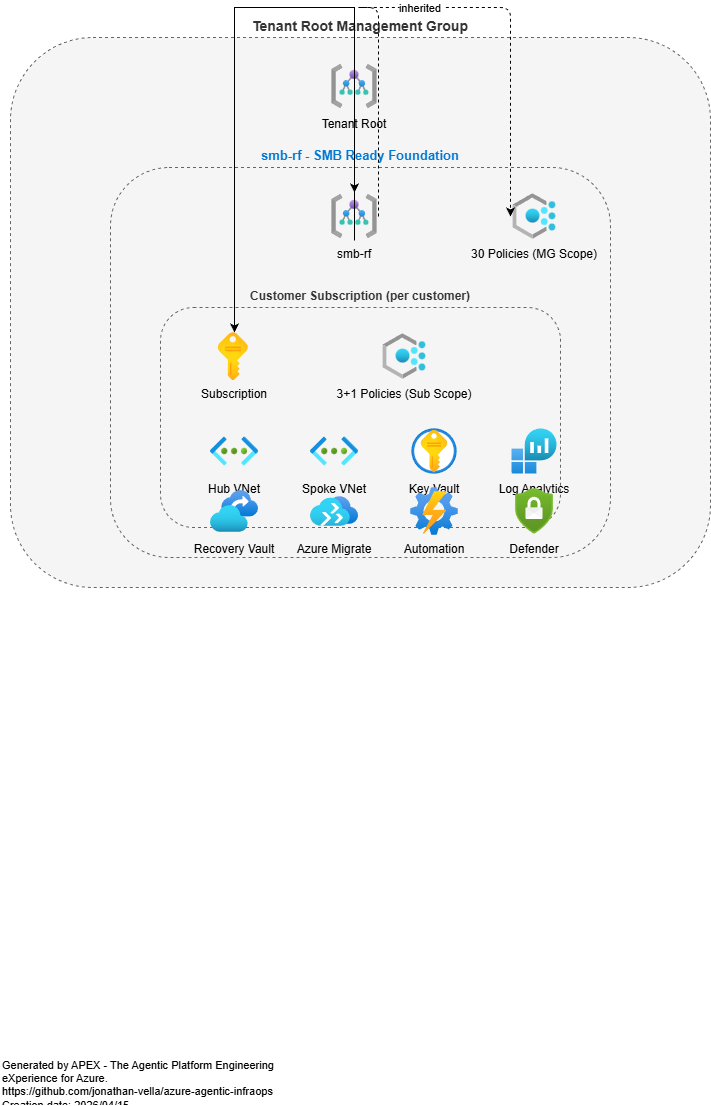 Management group hierarchy: Tenant Root → smb-rf → target subscription
Management group hierarchy: Tenant Root → smb-rf → target subscription